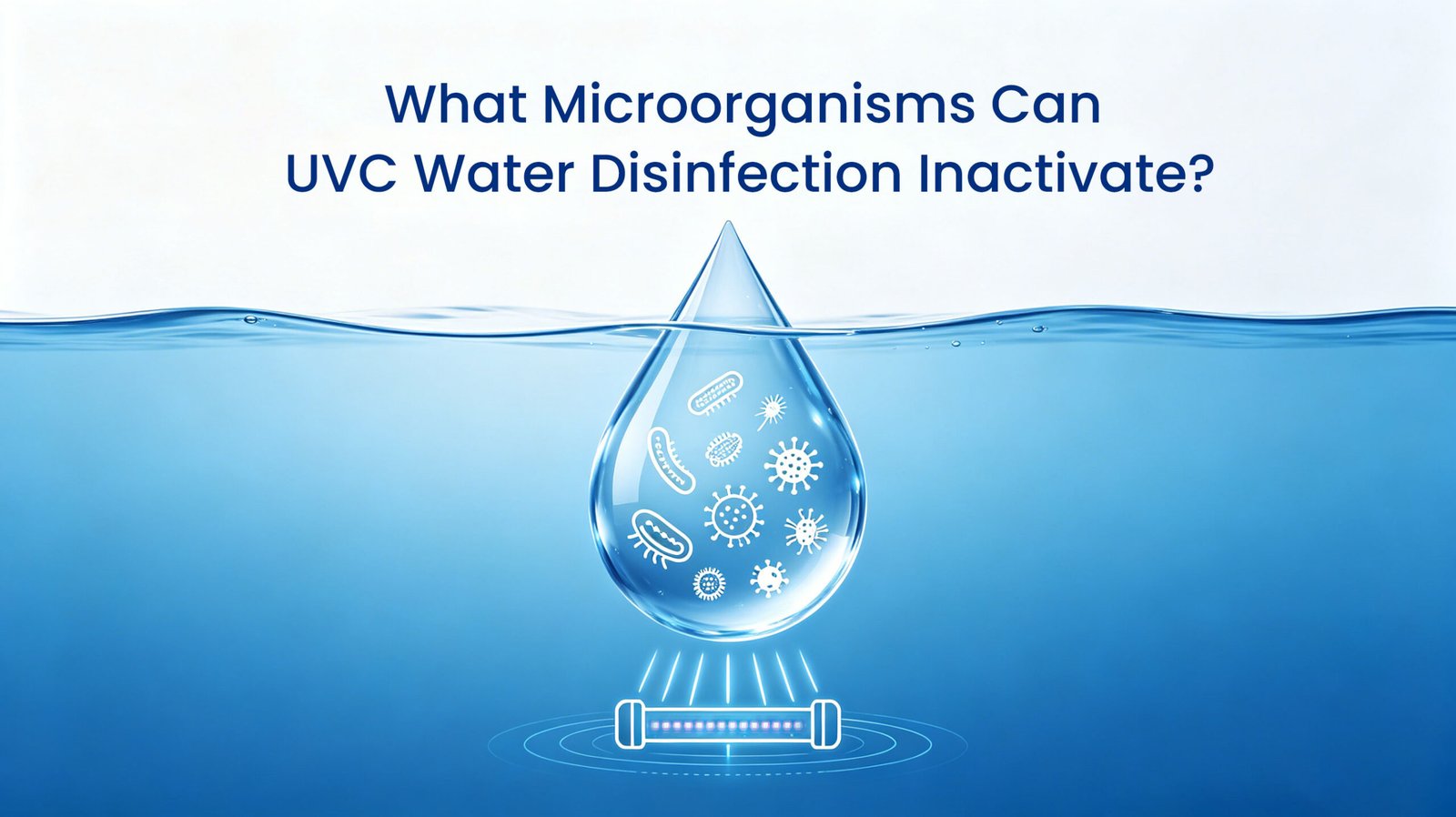
This article explains how UVC water disinfection inactivates microorganisms in water, including bacteria, viruses, and protozoa. It...
UV‑C LED Water Purification Blog – UV Water Purification Insights & Practical UV‑LED Water Treatment Guides for Home and Commercial Use.
This article explains how UVC water disinfection inactivates microorganisms in water, including bacteria, viruses, and protozoa. It...

With only 3% of the world's water being fresh, the efficient recycling of greywater has become a...
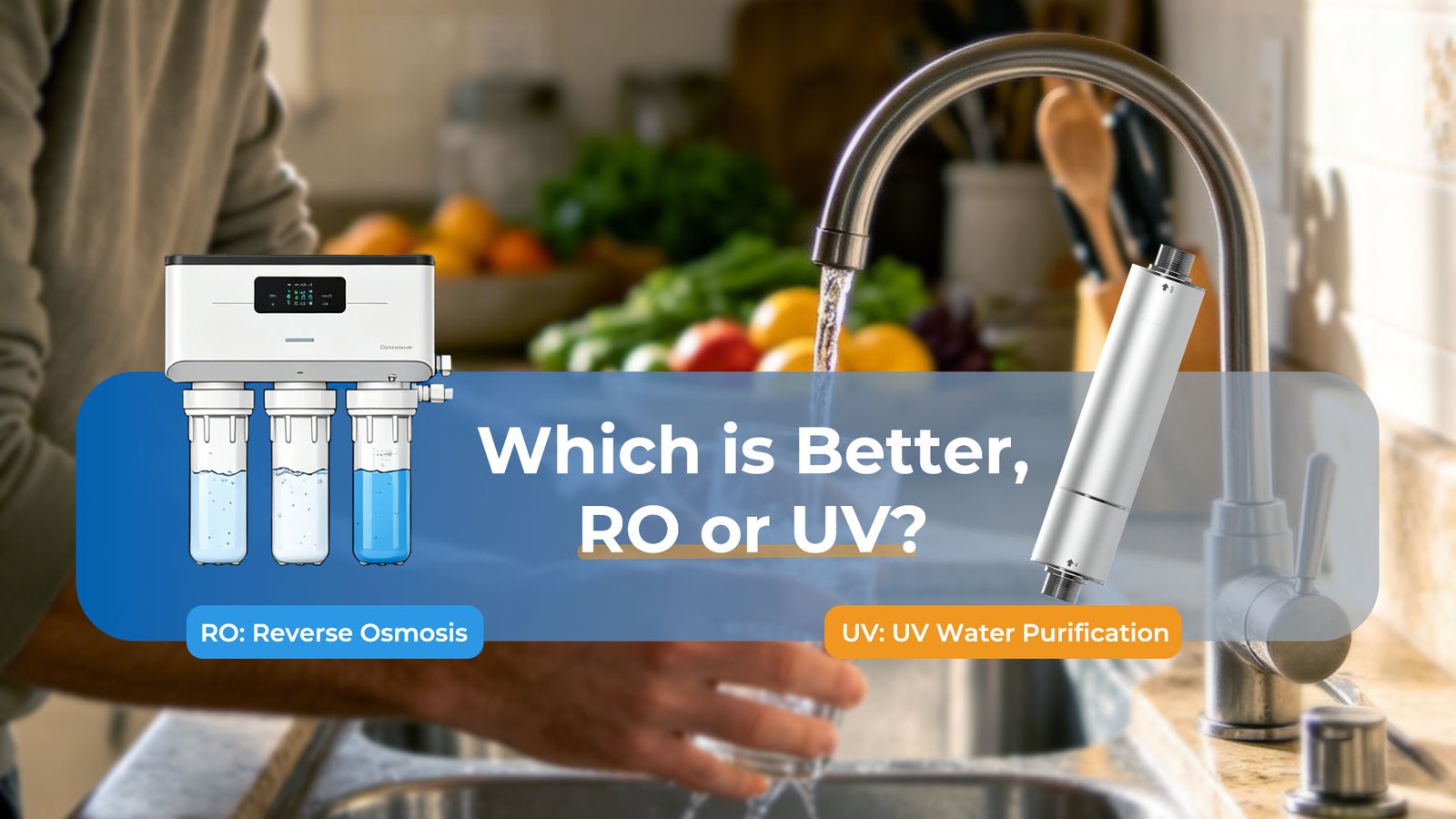
"This article is designed to help consumers make informed decisions when selecting a water purification solution. It...

This article explores the major types of water pollutants—biological, chemical, and physical—and their associated health risks, including...
This article explores the shift from traditional mercury-based UV lamps to compact, high-efficiency UVC LED technology for...

Single Events Bolg Does UVC LED Affect Water Taste? The Truth About Modern Water Disinfection Drinking water...
Single Events Bolg What Is UVC LED? A Complete Guide to Deep-Ultraviolet Disinfection UVC LED is a...

UVC LED is an ideal final disinfection solution for under-sink RO water purifiers. While RO membranes effectively...
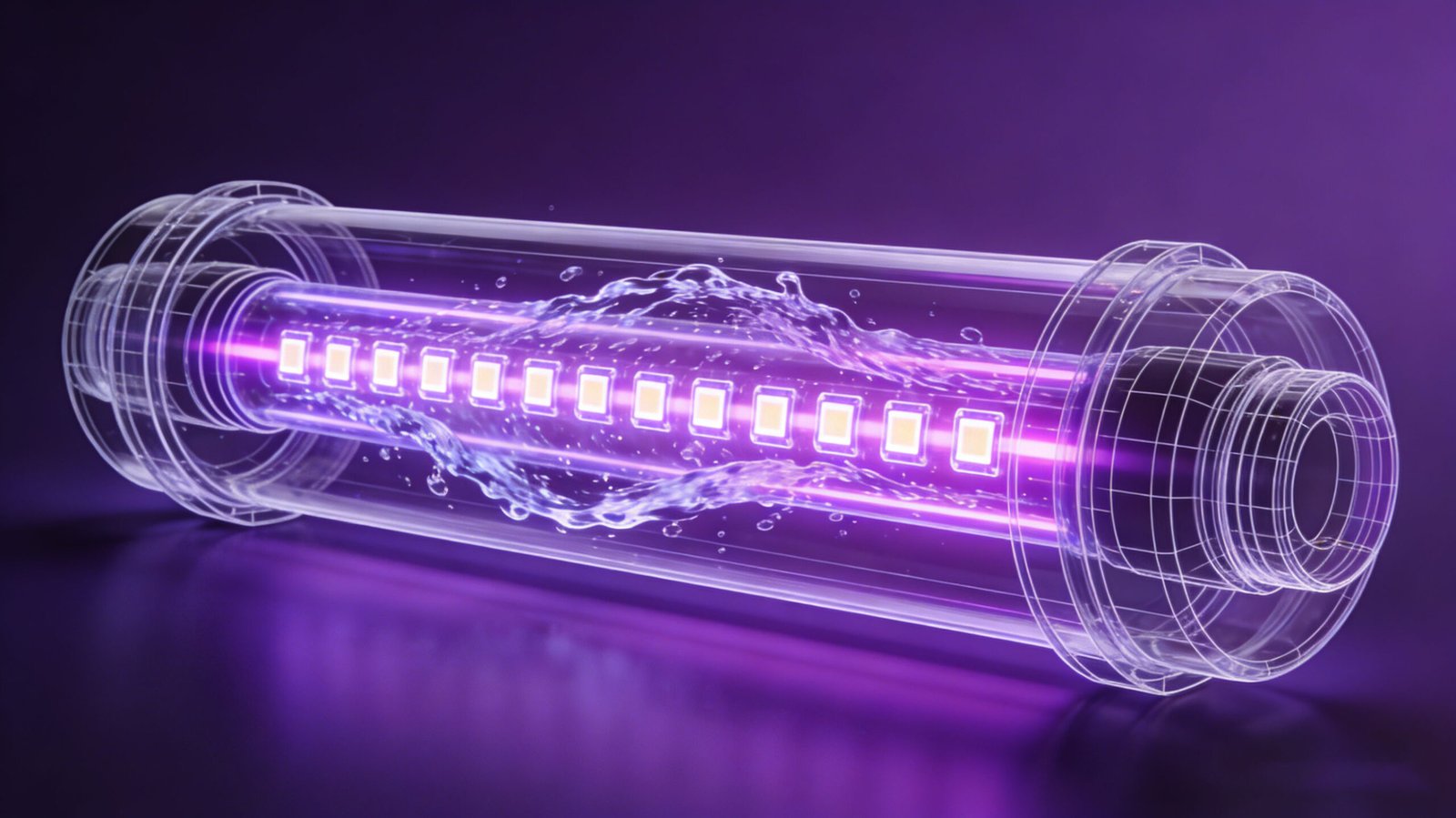
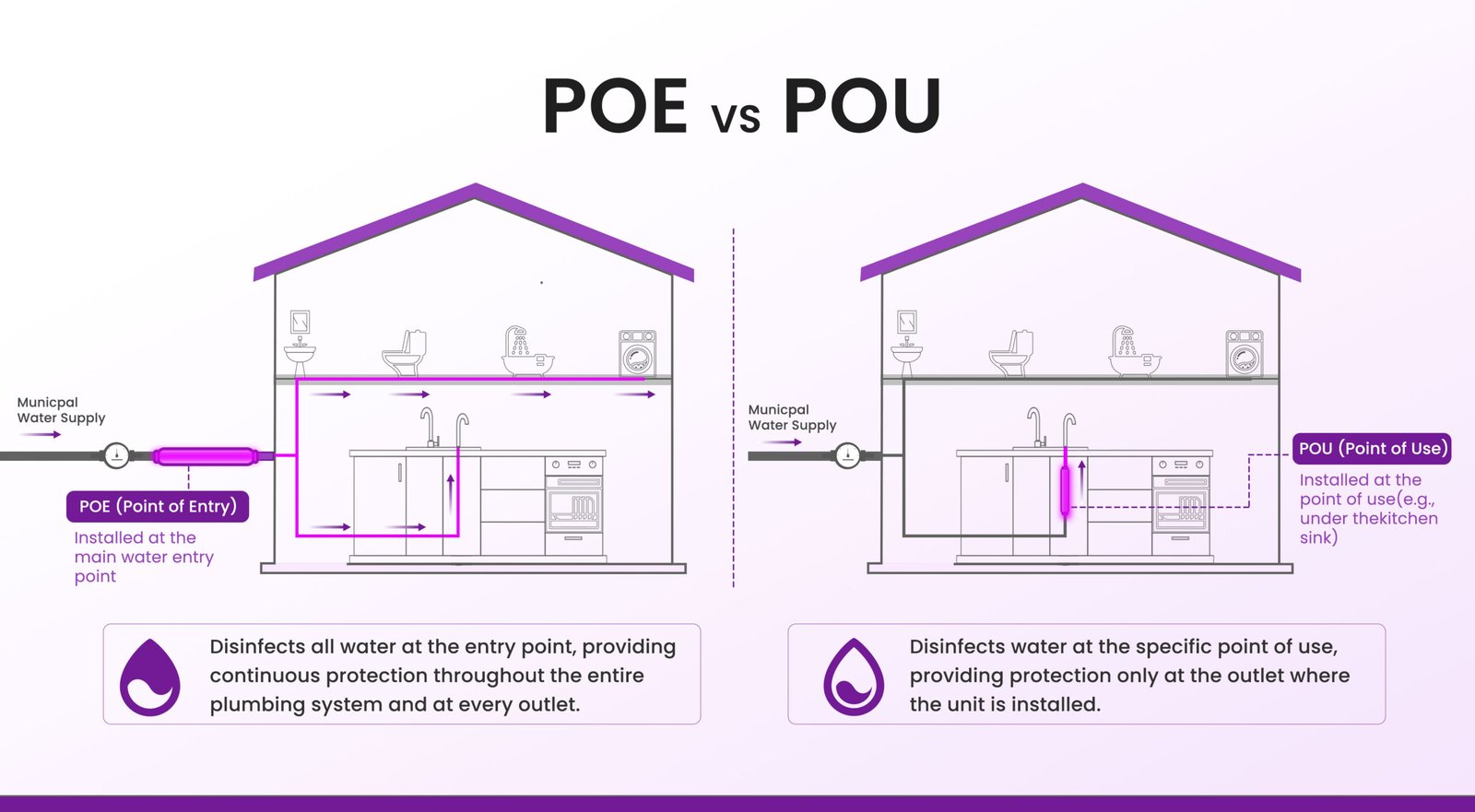
INSTAUV’s UVC LED Water Disinfection System is a compact, mercury-free, inline end-point (point-of-use) sterilization solution designed for...
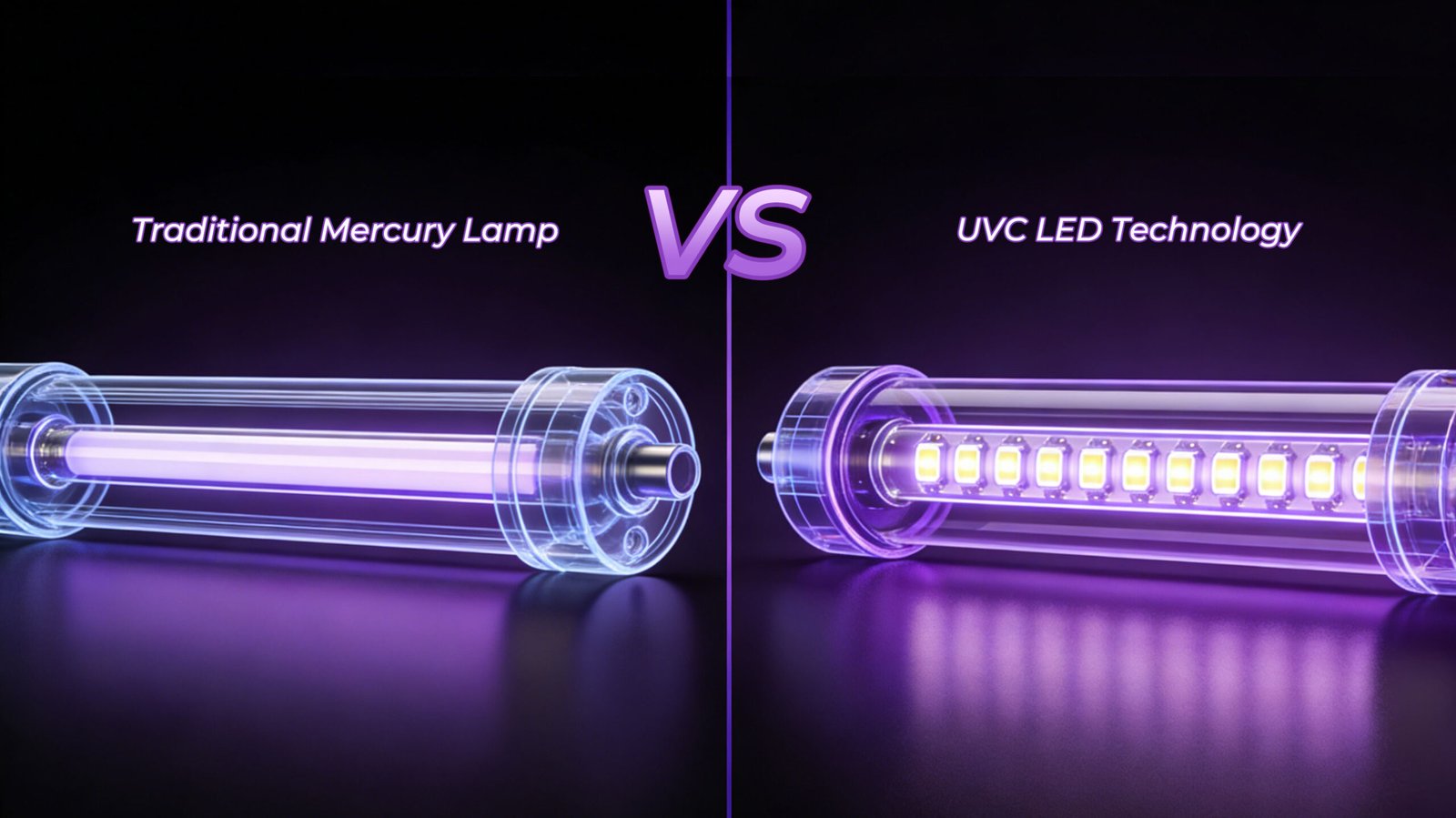
INSTAUV’s UVC LED Water Disinfection System marks a major upgrade over traditional mercury UV lamps. It delivers...

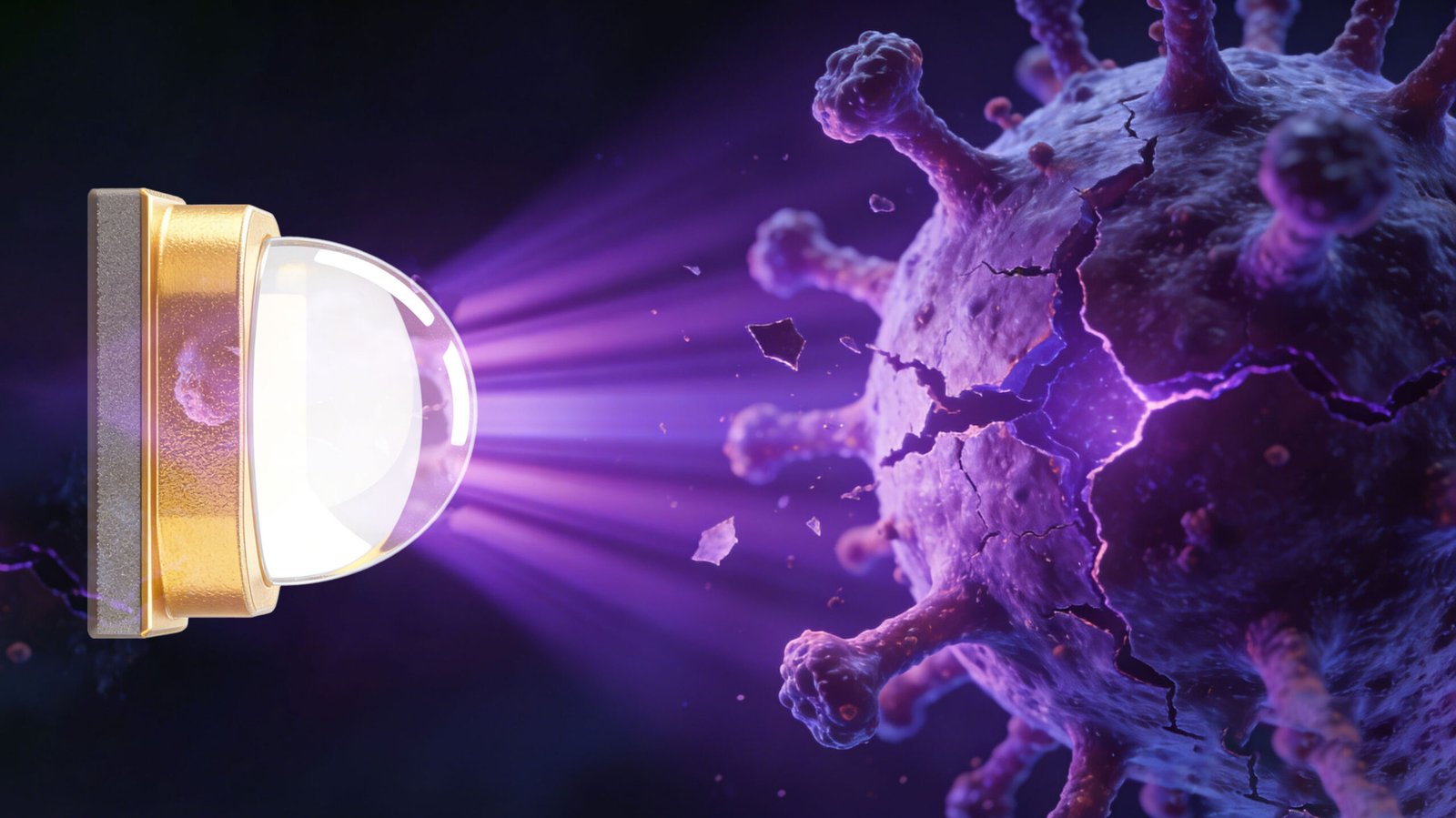
UVC LED water disinfection is an advanced, chemical‑free technology that uses short‑wavelength ultraviolet light (typically 260–280 nm)...

Be the first to get our R&D updates, case studies, and engineering resources—subscribe now.
© 2026 INSTAUV LLC. All Rights Reserved.
We’re here to help! Reach out with any questions you may have.